
 University of Kansas
University of Kansas
I am a final-year PhD candidate in Computer Science at the University of Kansas, advised by Dr. Fengjun Li and Dr. Bo Luo.
My research primarily focuses on Physical AI systems and their security. Specifically, I investigate both offensive and defensive techniques for mobile, CPS, and AI-enabled systems.
My research interests include:
• Trustworthy ML/AI: Adversarial ML; Prompt injection; AI misinformation and misuse.
• Physical AI: IoT/CPS; Mobile; Wireless Systems; Side and Covert channels
• Communication security: NFC; Optical fiber communication; GPS spoofing.
Before joining KU, I received my B.S. and M.Eng. degrees from Beihang University. After graduation, I worked as a full-time research scientist at the Institute of Information Engineering, Chinese Academy of Sciences.
News | Education | Research Experience | Honors & Awards | Teaching Experience | Selected Publications
Warning
Problem: The current name of your GitHub Pages repository ("Solution: Please consider renaming the repository to "
http://".
However, if the current repository name is intended, you can ignore this message by removing "{% include widgets/debug_repo_name.html %}" in index.html.
Action required
Problem: The current root path of this site is "baseurl ("_config.yml.
Solution: Please set the
baseurl in _config.yml to "News
Education
-
 University of KansasDepartment of Electrical Engineering and Computer Science
University of KansasDepartment of Electrical Engineering and Computer Science
Ph.D. Candidate in Computer ScienceJan. 2020 - present -
 Beihang UniversitySchool of Instrumentation Science and Optoelectronic Engineering
Beihang UniversitySchool of Instrumentation Science and Optoelectronic Engineering
M.Eng. in Optical Engineering
Advisor: Prof. Xiaxiao WangSep. 2011 - Mar. 2014 -
 Beihang UniversitySchool of Instrumentation Science and Optoelectronic Engineering
Beihang UniversitySchool of Instrumentation Science and Optoelectronic Engineering
B.S. in Electronic Engineering
Advisor: Prof. Zhongyi ChuSep. 2007 - Jul. 2011
Research Experience
-
 Institute for Information Science (I2S), University of Kansas(KU)Graduate Research AssistantJan. 2020 - present
Institute for Information Science (I2S), University of Kansas(KU)Graduate Research AssistantJan. 2020 - present -
 Institute of Information Engineering (IIE), Chinese Academy of Sciences (CAS)Assistant Research FellowMar. 2014 - Dec. 2019
Institute of Information Engineering (IIE), Chinese Academy of Sciences (CAS)Assistant Research FellowMar. 2014 - Dec. 2019 -
 Institute of Optoelectronics Technology, Beihang UniversityGraduate Research AssistantSep. 2011 - Mar. 2014
Institute of Optoelectronics Technology, Beihang UniversityGraduate Research AssistantSep. 2011 - Mar. 2014
Selected Honors & Awards
-
NDSS Fellow (1 of 20 worldwide) - Internet Society2026
-
Doctoral Student Research Fund Award (30 annually) - KU2025
-
DAVID D. and MILDRED H. ROBB AWARD - KU2024, 2025
-
ACM CCS Travel Grant Award (about 1 of 30 worldwide) - ACM SIGSAC2024
-
Graduate Engineering Association Award - KU2024, 2025
-
Graduate Student Travel Fund - KU Student Senate2024, 2025
-
The second prize of the Science and Technology Award (ranked 2nd) - MIIT (PRC)2019
-
Annual Outstanding Researcher Award (20 out of 690) - IIE, CAS2018
-
Annual Outstanding Researcher Award (4 out of 80) - 4th research department, IIE, CAS2016
-
Outstanding Master’s Thesis Award - Beihang University2014
-
Science and Technology Award - Ministry of Education (PRC)2013
-
Graduate Guanghua Scholarship - Beihang University2013
-
Outstanding Undergraduate Thesis Award - Beihang University2011
Teaching Experience
-
EECS 569 - Computer ForensicsFall 2024
-
EECS 565 - Introduction to Information and Computer SecurityFall 2025, 2024, 2023
-
EECS 447 - Introduction to Database SystemsSpring 2026, 2024, 2023
-
EECS 268 - Programming IISpring 2025
Selected Publications (view all )
PhantomSeal: Proactive Deepfakes Defense with Identity/Context Protection and Forensic Tracing
Liangqin Ren, Zeyan Liu, Ye Wang, Yuxin Chen, Fengjun Li, Bo Luo
The ACM Conference on Computer and Communications Security (CCS) Accepted. 2026
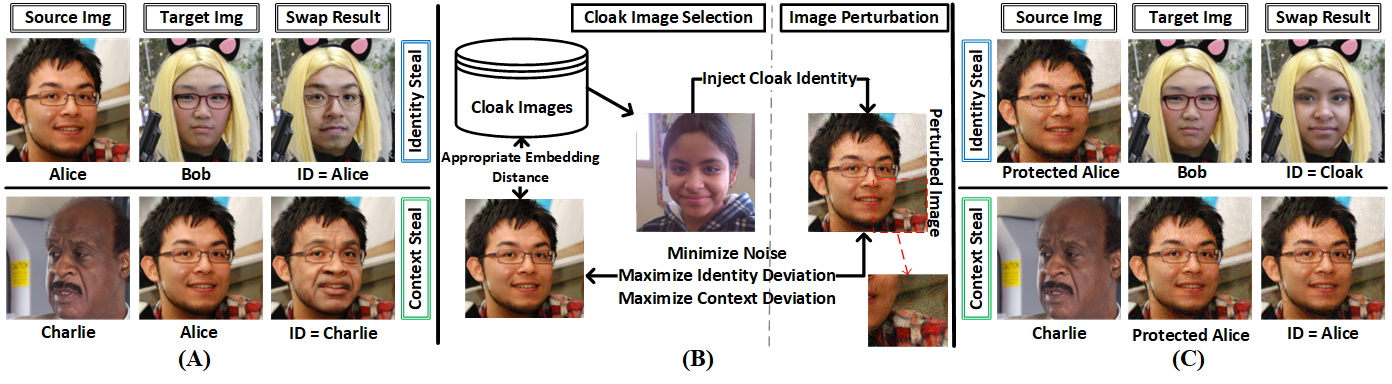
In this paper, we present PhantomSeal, the first proactive defense to simultaneously protect both the identity and the context of users' images from being used in face-swapping attacks, while supporting forensic tracing.
PhantomSeal: Proactive Deepfakes Defense with Identity/Context Protection and Forensic Tracing
Liangqin Ren, Zeyan Liu, Ye Wang, Yuxin Chen, Fengjun Li, Bo Luo
The ACM Conference on Computer and Communications Security (CCS) Accepted. 2026
In this paper, we present PhantomSeal, the first proactive defense to simultaneously protect both the identity and the context of users' images from being used in face-swapping attacks, while supporting forensic tracing.
Side Meets Covert Channels: A Practical Fully Sensor-Driven Attack Chain.
Ye Wang, Yuying Li, Bo Luo, Fengjun Li
International Conference on Information and Communications Security (ICICS) Accepted. 2026
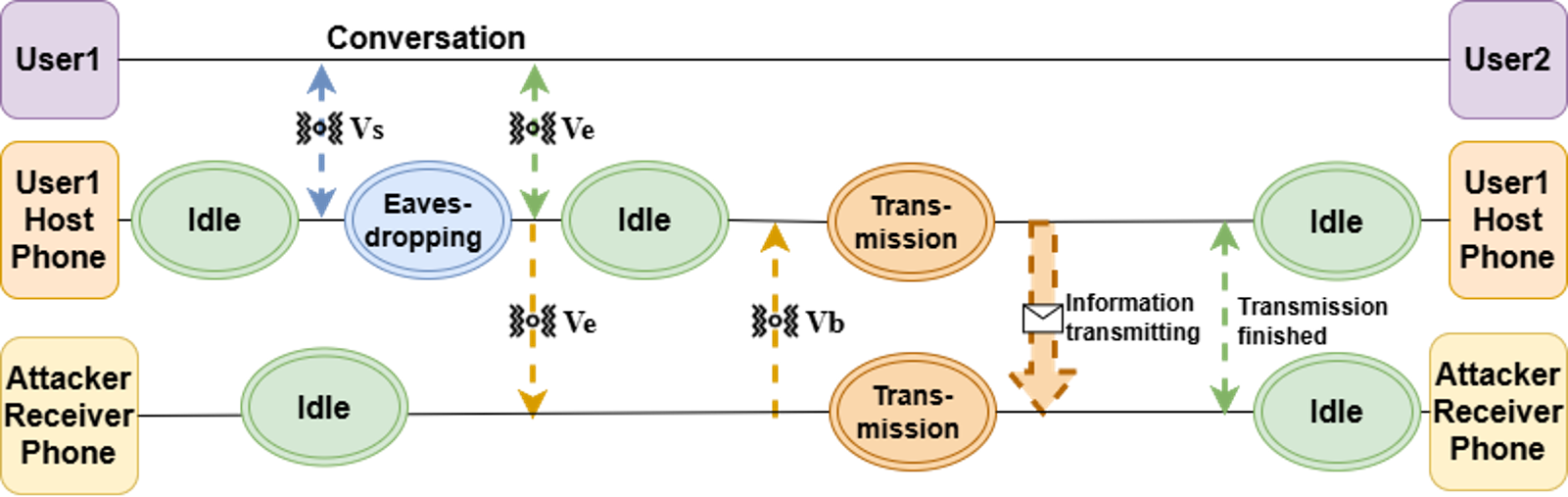
In this paper, we first explore the control plane of sensor-based attacks and leverage a lightweight control protocol to demonstrate how to rebuild the practicality of side-channel and covert-channel attacks on modern smartphones.
Side Meets Covert Channels: A Practical Fully Sensor-Driven Attack Chain.
Ye Wang, Yuying Li, Bo Luo, Fengjun Li
International Conference on Information and Communications Security (ICICS) Accepted. 2026
In this paper, we first explore the control plane of sensor-based attacks and leverage a lightweight control protocol to demonstrate how to rebuild the practicality of side-channel and covert-channel attacks on modern smartphones.
Beyond Conventional Triggers: Auto-Contextualized Covert Triggers for Android Logic Bombs
Ye Wang, Bo Luo, Fengjun Li
Network and Distributed System Security Symposium (NDSS) 2026
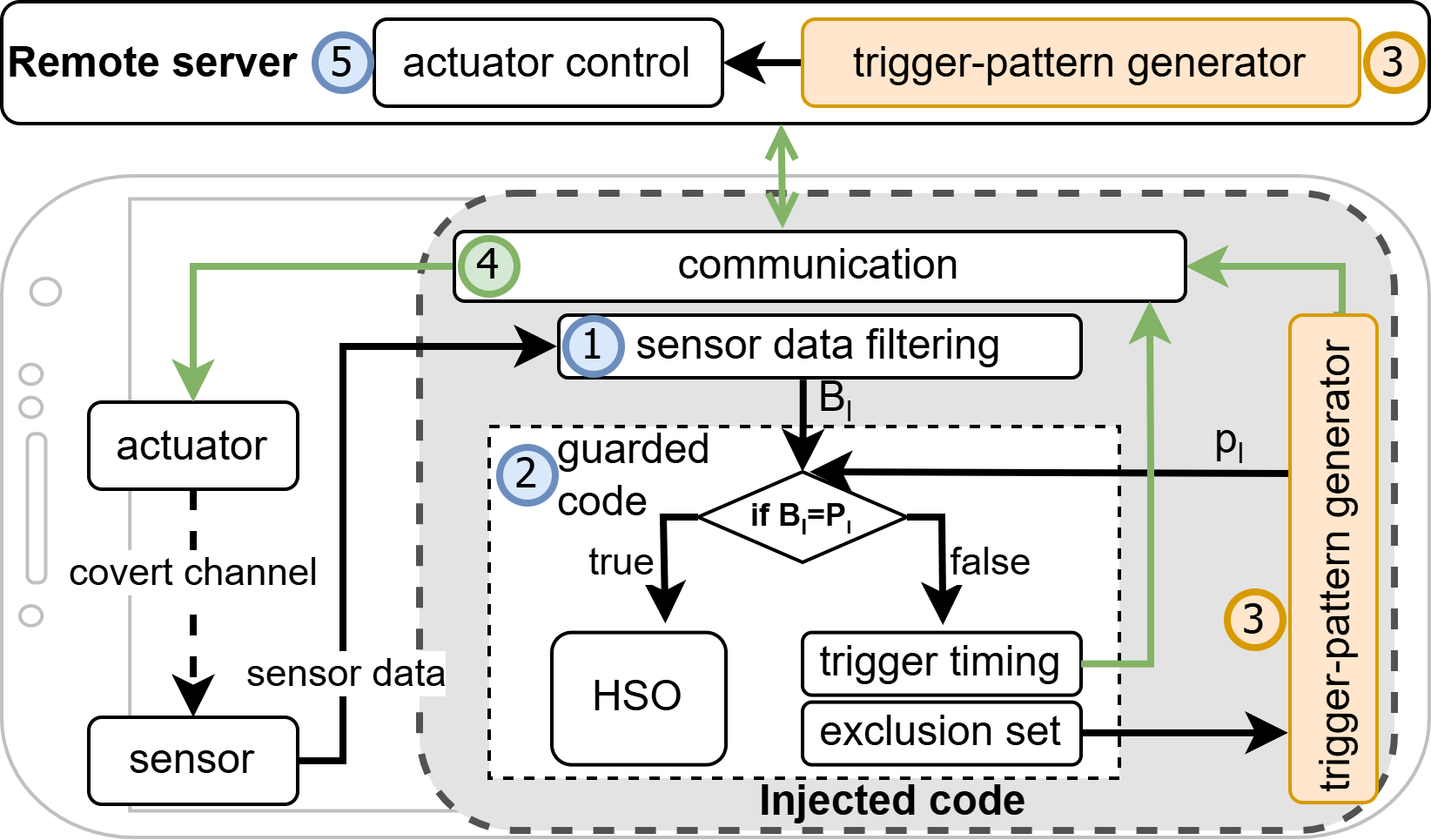
In this paper, we present SensorBomb, a logic-bomb framework that leverages auto-contextualizing triggers within an app’s legitimate sensor usage, actuator behaviors, and functional context, using onboard sensor–actuator covert channels and dynamically adapted trigger patterns to evade analysis, fuzzing, anomaly detection, and user suspicion.
Beyond Conventional Triggers: Auto-Contextualized Covert Triggers for Android Logic Bombs
Ye Wang, Bo Luo, Fengjun Li
Network and Distributed System Security Symposium (NDSS) 2026
In this paper, we present SensorBomb, a logic-bomb framework that leverages auto-contextualizing triggers within an app’s legitimate sensor usage, actuator behaviors, and functional context, using onboard sensor–actuator covert channels and dynamically adapted trigger patterns to evade analysis, fuzzing, anomaly detection, and user suspicion.
The Invisible Polyjuice Potion: an Effective Physical Adversarial Attack against Face Recognition
Ye Wang, Zeyan Liu, Bo Luo, Rongqing Hui, Fengjun Li
Proceedings of the 2024 on ACM SIGSAC Conference on Computer and Communications Security (CCS) 2024
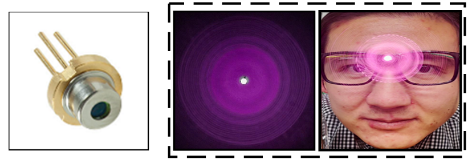
In this paper, we propose a novel physical adversarial attack against deep face recognition systems, namely Agile (Adversarial Glasses with Infrared LasEr). It generates adjustable, invisible laser perturbations and emits them into the camera CMOS to launch dodging and impersonation attacks against facial biometrics systems.
The Invisible Polyjuice Potion: an Effective Physical Adversarial Attack against Face Recognition
Ye Wang, Zeyan Liu, Bo Luo, Rongqing Hui, Fengjun Li
Proceedings of the 2024 on ACM SIGSAC Conference on Computer and Communications Security (CCS) 2024
In this paper, we propose a novel physical adversarial attack against deep face recognition systems, namely Agile (Adversarial Glasses with Infrared LasEr). It generates adjustable, invisible laser perturbations and emits them into the camera CMOS to launch dodging and impersonation attacks against facial biometrics systems.